cyber security
-
Posted: July 14, 2022Read more
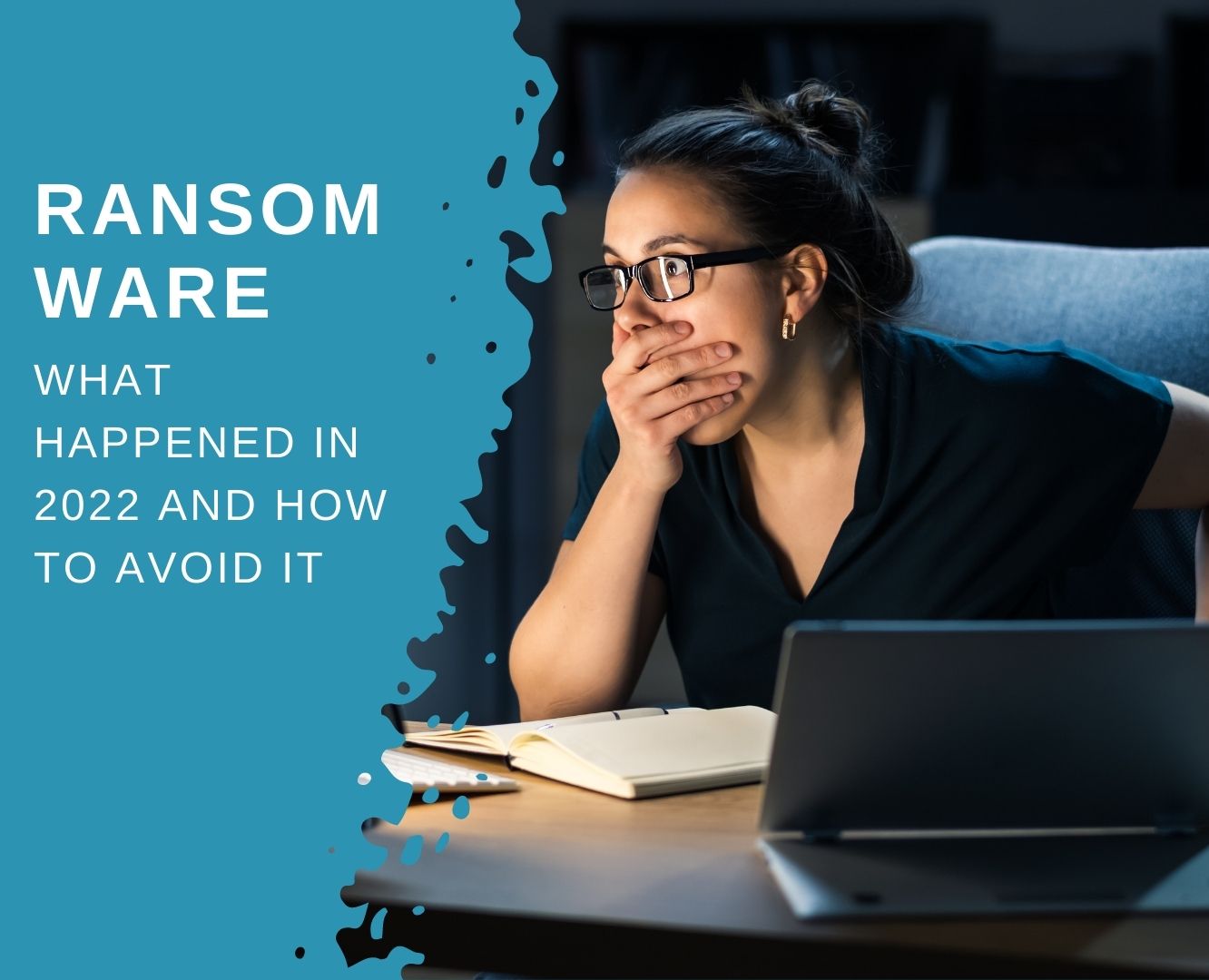
الفدية Ransomware وسيلة شائعة لمجرمي الإنترنت للاستفادة من أنشطتهم. يستخدمون برامج الفدية لتشفير البيانات الأساسية للشركات ويطلبون دفع فدية في المقابل. إذا لم تقم الشركات بعمل نسخة احتياطية من معلوماتها ، فيجب عليها البحث في جيوبها لاستعادتها.
-
Posted: November 19, 2021Categories: Cyber SecurityRead more
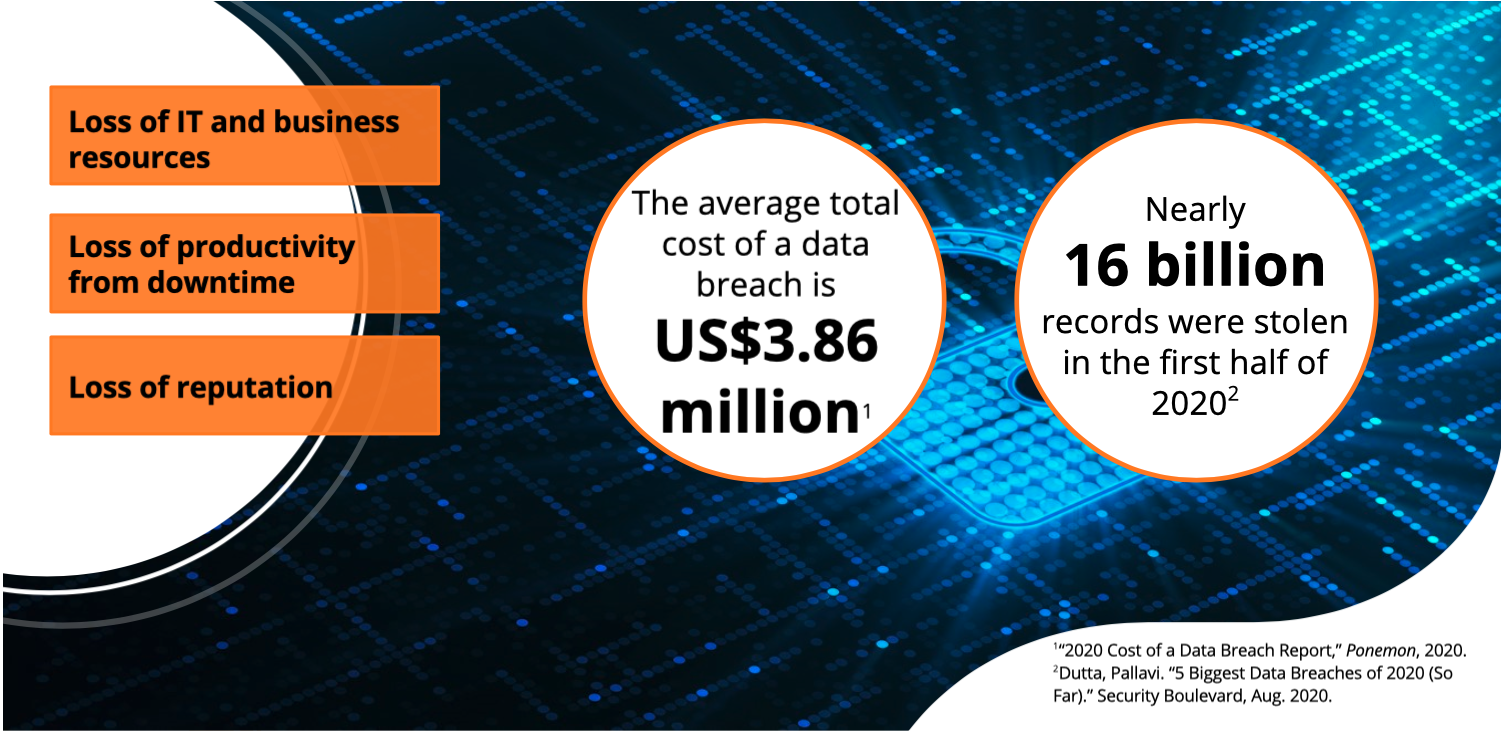
If security is not top of mind for your customers, it should be. Security breaches can be disastrous for IT and for the business as a whole. Victims of ransom ware and other malware attacks may need to pay large sums of cash or spend considerable IT resources to recover and get the network up and running. These breaches can result in a loss of productivity from downtime, and can even stop business. Breaches can also permanently damage the company's reputation and future sales. When personal information is stolen, lawsuits and loss of customers can continue to harm companies long after the breach.
-
Posted: August 09, 2021Categories: Cyber SecurityRead more
As cyber threats become ever more complex, the pressure to have the right endpoint solution in place has also grown. However, the endpoint security marketplace has become congested with many different solutions, and is so full of indefensible marketing claims that making an educated decision for your organization is increasingly difficult. This guide provides clarity by walking you through the key endpoint security technologies to ensure you have the right protection in place. It also enables you to see how different vendors stack up in independent tests, helping you make an informed choice.
The uncomfortable truth about endpoint security
The endpoint security market is full of hype and extravagant claims. However, the reality is that 68% of organizations fell victim to a cyberattack in the last year1. That’s why world-class protection is the foundation of any effective security strategy. However, protection alone is not enough. Four out of five organization admit having a shortage of internal security expertise1. With this in mind usability is also essential if hard-pressed IT teams are to make best use of the protection capabilities. You should also assume that a threat will get through your defenses and equip your organization accordingly. This includes having full visibility into how threats enter the organization, where they went, and what they touched so that you can neutralize the attack and plug any security gaps. Use this guide to understand the protection technologies available and make and informed choice of endpoint protection products.
Product Features and Capabilities
Endpoint security solutions, sometimes referred to simply as antivirus solutions, may include a variety of foundational (traditional) and modern (next-gen) approaches to preventing endpoint threats. W